The Bible has been translated into numerous languages, yet its original language is ancient Hebrew. Many have sought a biblical code or cipher believed to contain divine meaning.
And indeed, there are numerous examples of secrets found in the Bible that can be revealed using a decryption method.
This article will not delve into those theories or methods. This subject has been extensively covered in research. I’d like to explore a less obvious topic: the way modern cryptography is presented in the Bible.
As a software engineer with extensive experience in modern cryptology and ciphering algorithms, I was astonished to discover that some of the most complex methods developed in the 20th century were already present in the Bible.
Therefore, I will use simple language to describe some cryptography techniques and highlight relevant biblical references.
Cryptography for dummies
Goal of cryptography
Cryptography is the practice of sending confidential text or data to another person in a way that only the recipient can read it. Any person in the middle, including the messenger, should not be able to understand the message.
Terminology
- Cipher – a cipher is a method (algorithm) that dictates how a piece of text is encrypted and decrypted. For example, a common cipher is the method of switching letters according to some replacement table.
- Key/Secret – the key is what is used to encrypt and to decrypt the message. Without the key, the message cannot be read. The sender of the message needs to make sure that the recipient has the key to open and read the message. For example, in a letter switching method, the replacement table is the Key. The army uses this method and changes the table every two weeks.
- Identification – because the Key for decryption should be kept secure, the sender of the message also wants to make sure that the recipient got the Key, and not anybody else. Because if the Key falls into the wrong hands, all messages are breached. Therefore, the sender wants to identify the person to whom he hands the key.
- Password/Passcode – this is the same as Key, but it is more often used for authentication (Identification). So when I, as a sender, want to verify the receiver’s identity, I ask him to use a password as an identification method. After successful authentication, I give him the key to decipher messages that I will send in the future. So we have doubled our security.
After this technical introduction, let’s see how all this appears in the Bible.
Gematria (Hebrew: גמטריא)
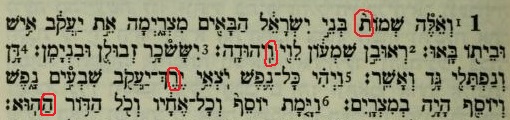
This is the simplest type of cipher. In the Hebrew alphabet, every letter has a numeric value. Aleph:א = 1, Bet:ב = 2, Gimel:ג = 3, etc.
All the chapters and verses in the Hebrew Bible are numbered by letters and not by numbers. So Genesis 1:1 is numbered: א:א. Psalms 114 is numbered: קיד.
The cipher here is a translation table that links numbers to letters. Given its non-confidential nature, the details have been disseminated to all parties.
Gematria is used a lot in Kabbala, because each word can be translated into a number, and the numbers can be assessed according to numerology.
David and Jonathan
A real example of using a very unique cipher is the story of David and Jonathan. David suspected that Saul, Jonathan’s father, wanted to kill him. Jonathan, to comfort David, suggested how he would reveal to David whether the king wanted to kill him or not:
David would hide behind a rock. Jonathan, after hearing from his father in the palace, would send a secret message to David, so that no one should know that they had communicated with each other. Jonathan would shoot three arrows and would send his servant to find them. He would call the boy with a message that is the secret for David to know whether the king wants to kill him or not (1 Samuel 20).
In this story, we have a Cipher – this is the method that Jonathan and David agreed on to understand the message. There is a Key – that is the secret message that Jonathan sent when calling his servant. The servant himself is a messenger who did not have a key and, therefore, could not decipher the message.
But note that there is also a need here for Authentication: Jonathan knew David and passed the secret to him and him only. He did not give the secret to someone else, so the secret would not fall into the wrong hands.
God will provide the Key
On multiple occasions within the biblical narratives, messages were concealed and remained undeciphered. However, a single individual possessed the ability, the Key, to interpret the message. This person received the key straight from God.
Joseph’s interpretations of various dreams in Egypt serve as a prime illustration.
Daniel also interpreted Nebuchadnezzar’s dream. Here, the king had forgotten his dream, but Daniel was able to tell him precisely what it was and what it meant.
Daniel deciphered later another message that was not a dream. It was King Belshazzar’s vision:
4 They drank wine, and praised the gods of gold and silver, bronze and iron, wood and stone. 5 In the same hour the fingers of a man’s hand appeared and wrote opposite the lampstand on the plaster of the wall of the king’s palace; and the king saw the part of the hand that wrote.
…
25 “And this is the inscription that was written: MENE, MENE, TEKEL, UPHARSIN.
26 This is the interpretation of each word. MENE: God has numbered your kingdom, and finished it; 27 TEKEL: You have been weighed in the balances, and found wanting; 28 PERES: Your kingdom has been divided, and given to the Medes and Persians.” (Daniel 5:4-5, 26-28)
The message from God cannot be understood unless you have a key to it. Special chosen people receive the key, and only then can they decipher the message.

Give me the password!
5 The Gileadites captured the fords of the Jordan opposite Ephraim. And it happened when any of the fugitives of Ephraim said, “Let me cross over,” the men of Gilead would say to him, “Are you an Ephraimite?” If he said, “No,” 6 then they would say to him, “Say now, ‘Shibboleth.’” But he said, “Sibboleth,” for he could not pronounce it correctly. Then they seized him and slew him at the fords of the Jordan. Thus there fell at that time 42,000 of Ephraim. (Judges 12:5-6)
According to this story, the people of Gilead, led by Jephthah, were fighting against Ephraim. They could not distinguish one from the other – not by look or by language. But there was something about the people of Ephraim: They could not pronounce the word “Shibboleth” properly.
“Shibboleth” was the “Password” that was used for authentication.
Note that in this case, we call it “Biometric authentication“, because it is something the person has by nature and therefore can be easily tracked.
A side note here about the word “Shibboleth”(שִׁבֹּלֶת): Its meaning in Hebrew is “stalk of grain”. In Modern cryptography, this word is used to refer to “Password” and is even used as a trademark for an Identity Solution framework. Check it here: shibboleth.net

Forgot your password?
What would you do if you had forgotten your password? You need a way to reset it, right?
This happened to the people of Israel:
11 The whole vision has become to you like the words of a book that is sealed, which men deliver to one who is literate, saying, “Read this, please.”
And he says, “I cannot, for it is sealed.”
12 Then the book is delivered to one who is illiterate, saying, “Read this, please.”
And he says, “I am not literate.” (Isaiah 29:11-12)
When the Key or Password is lost, we are in trouble. We cannot read the encrypted messages. In his prophecy, Isaiah declares that this is what happened to the people of Israel.
In the past, they have had access to the Word of God. But now, they lost access and cannot read the book. Some of them are illiterate and cannot read; others can read, but the book is sealed, and they cannot open it. In both cases, the method – Cipher – is known, but the Key was lost.

Asymmetric cryptography
We go now to a further complication of cryptography: Asymmetric cryptography.
The idea is simple, but not the implementation.
Let’s assume that the one who writes the message and encrypts it, uses one private Key. But to decipher the message, the recipient needs a different key. A public key. The algorithm to implement this is very difficult, but feasible. Why do we need this?
Because if I have a private key that only I can encrypt a message, then anyone that accept the message and can decrypt it, knows for sure that it arrived from me, as I am the only one who holds the private key. In this case, the recipient wants to validate that the message is authentic and got from the right sender.
The key of the house of David
I will lay on his shoulder;
So he shall open, and no one shall shut;
And he shall shut, and no one shall open. (Isaiah 22:22)
This is a precise example of an asymmetric key set: The key of the house of David is the Private Key. It can open, and no one can close. It can close, and no one can open.
This same key appears again in The Book of Revelation.
These things says He who is holy, He who is true, He who has the key of David, He who opens and no one shuts, and shuts and no one opens. (Revelations 3:7)
